Risk Rating
Each vulnerability has a risk rating assigned. The following is a description of the different categories.
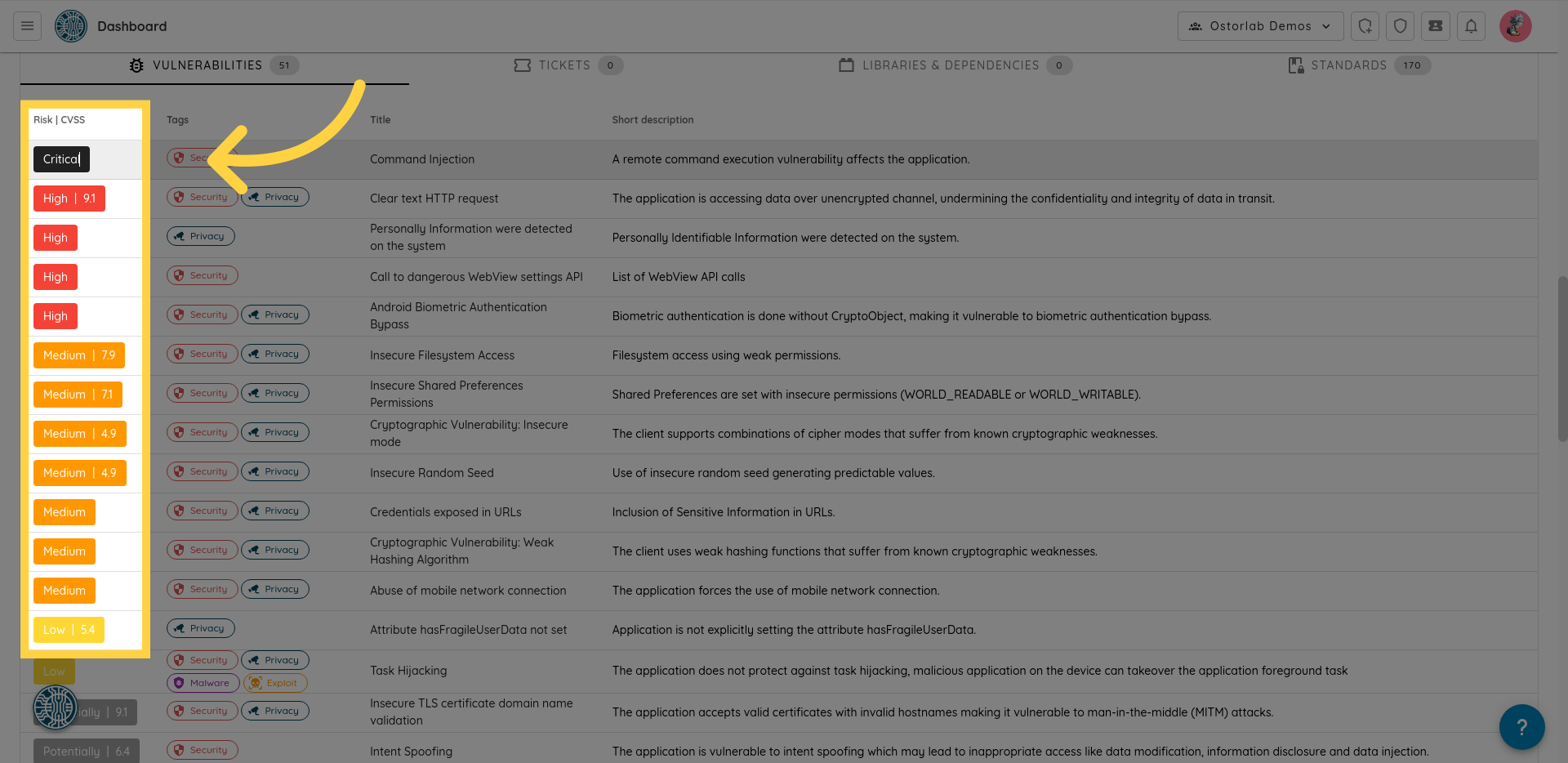
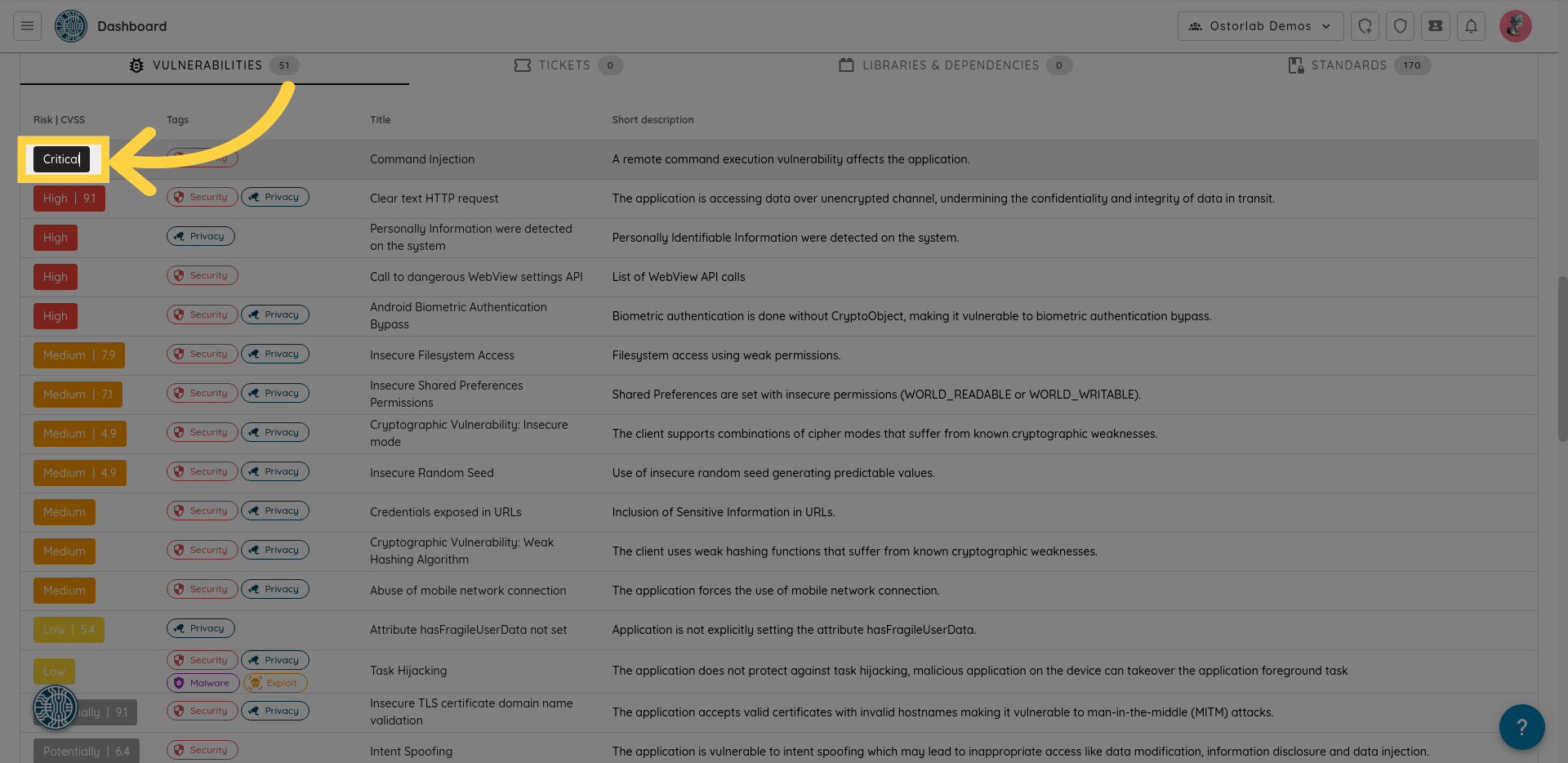
1. Critical
Critical vulnerabilities pose a severe threat to the system's security. Exploitation of these vulnerabilities could lead to significant damage, leakage of sensitive data, or complete system compromise.
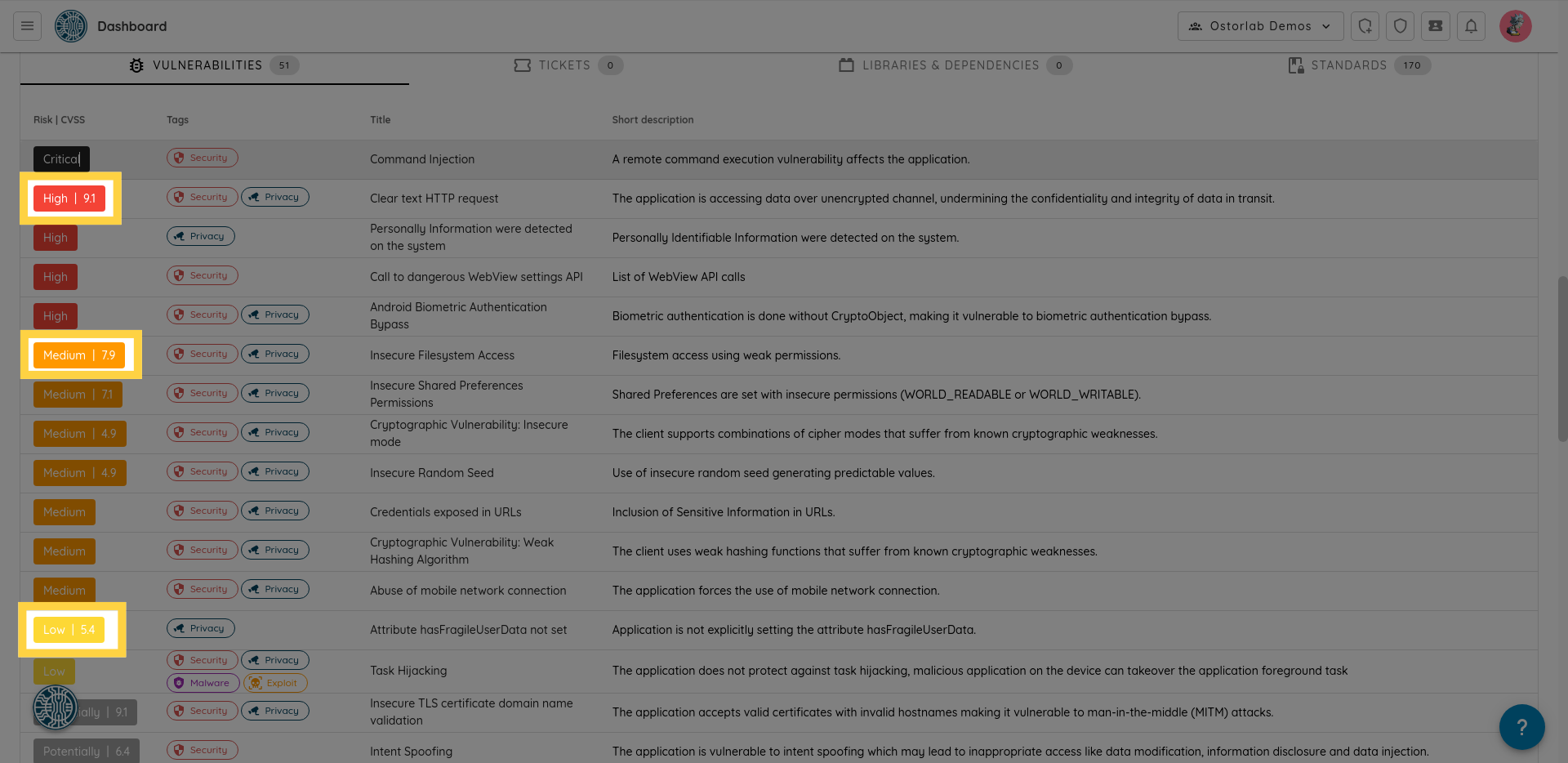
2. High, Medium and Low
High, Medium and Low vulnerabilities are confirmed vulnerabilities with a different score that considers the impact and complexity.
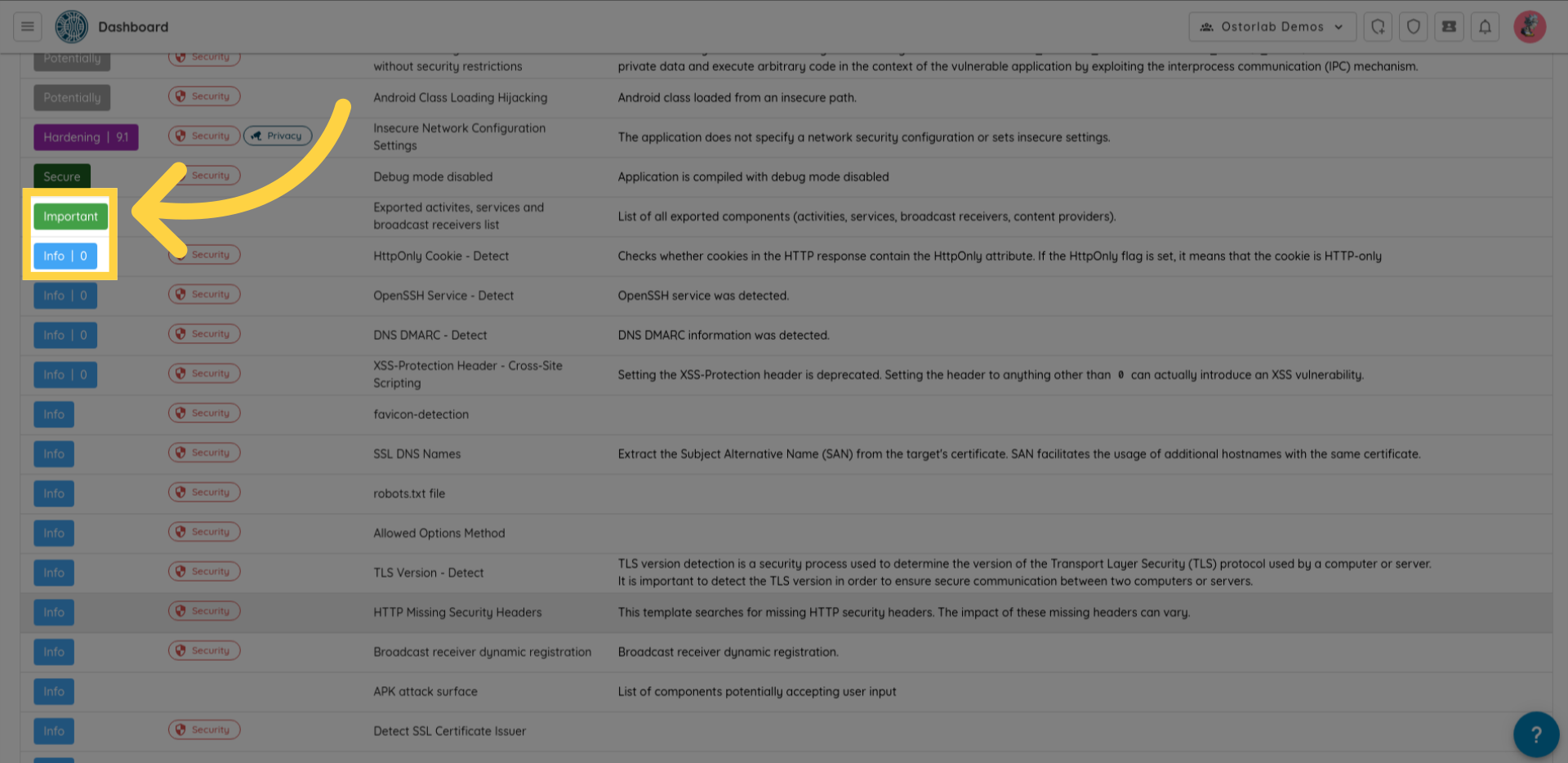
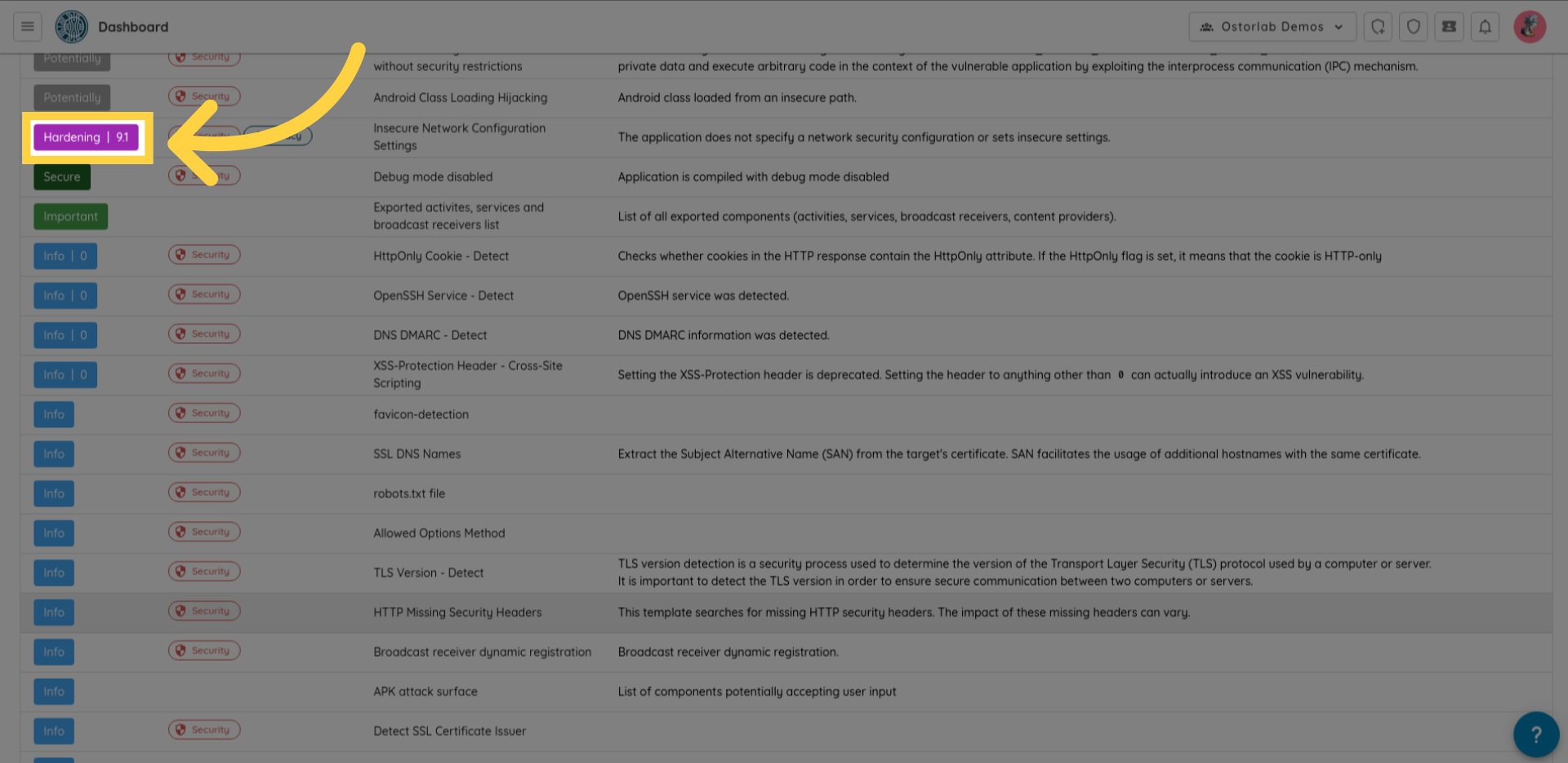
3. Hardening
The hardening findings highlights the absence of security measures that could prevent or mitigate the impact of certain vulnerabilities. This indicates a need for implementing security measures to enhance the overall security of the system.
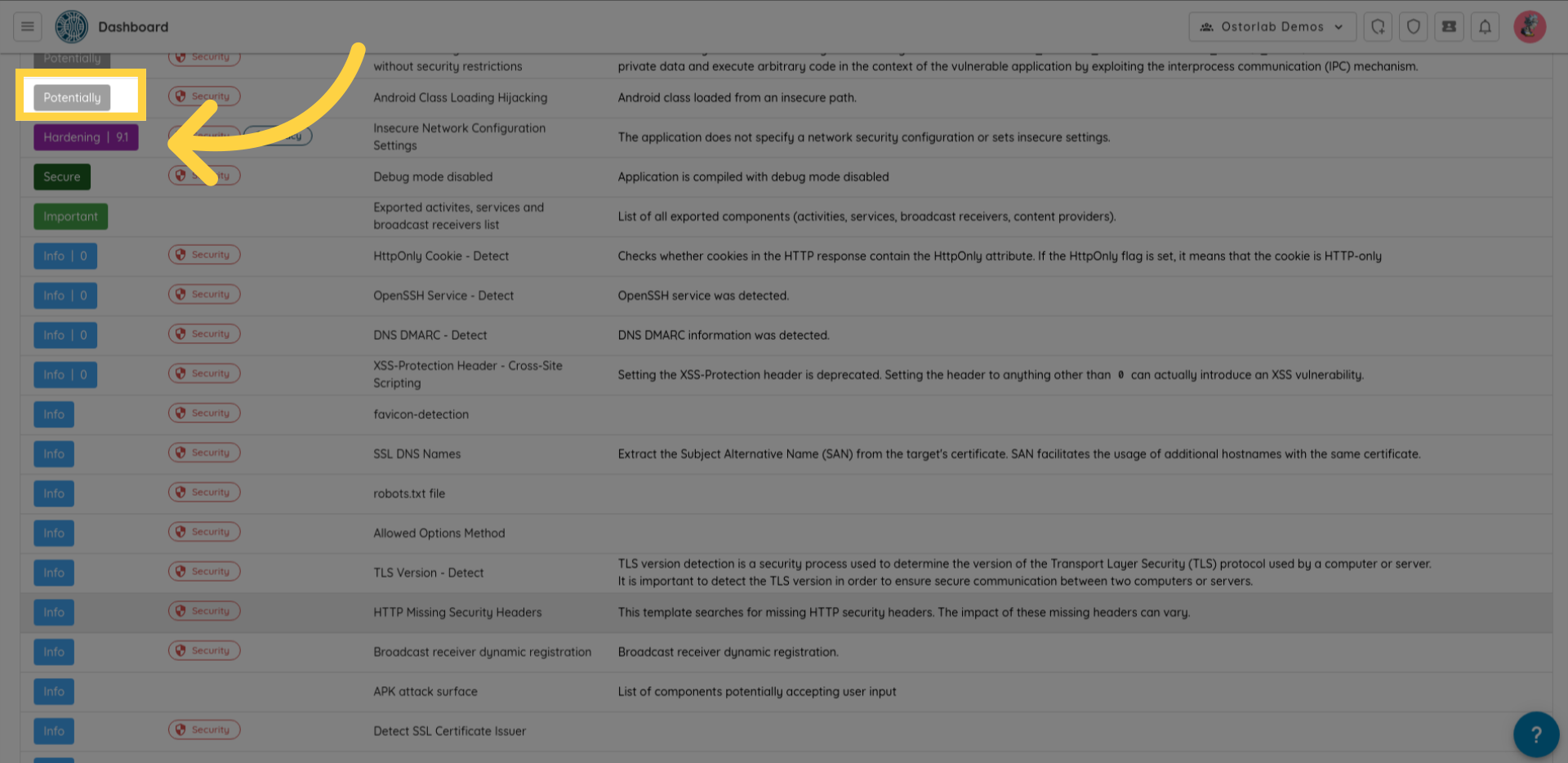
4. Potentially
Potentially findings are non-confirmed vulnerabilities that may depend on context and usage.
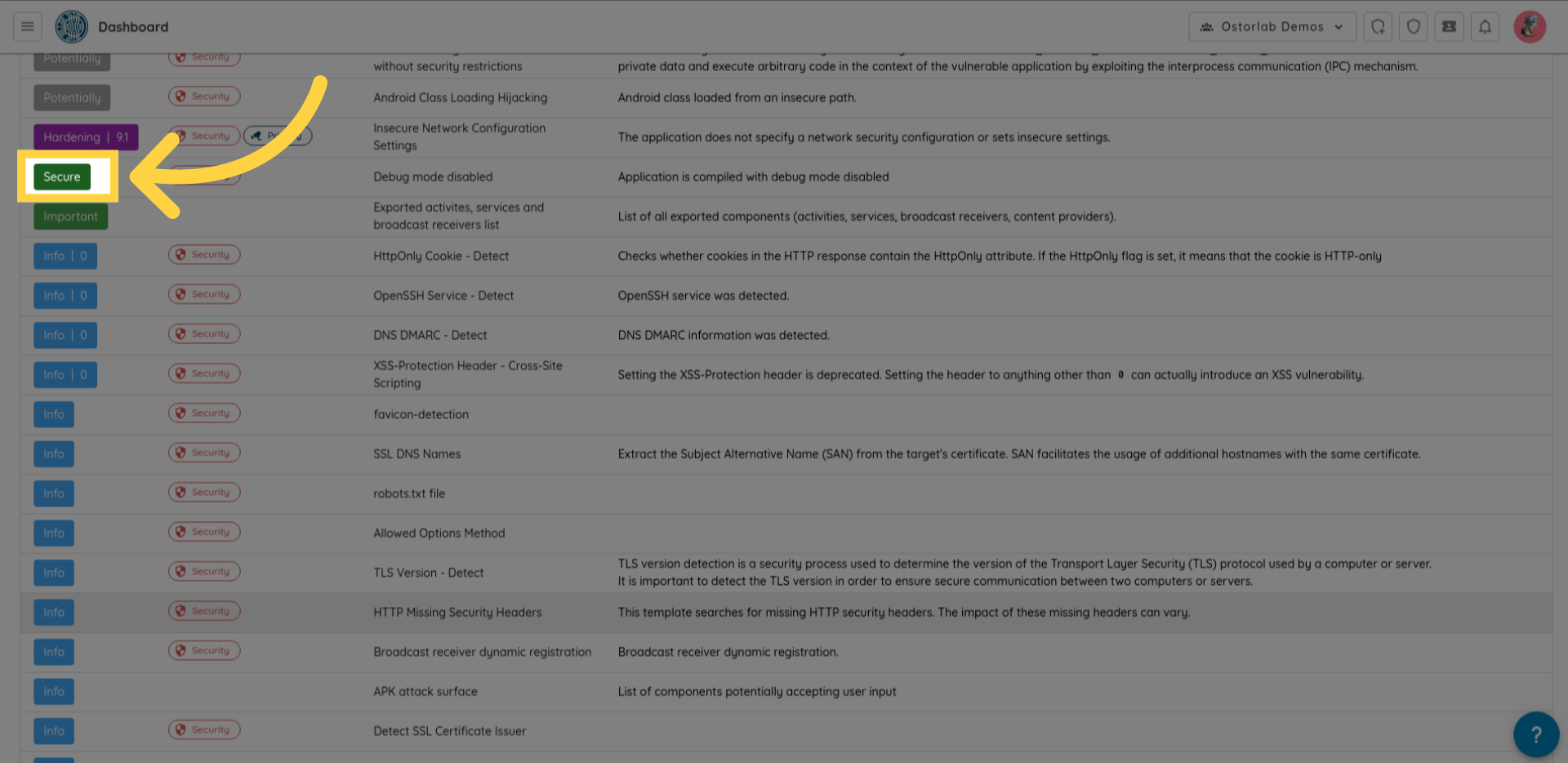
5. Secure
The secure findings indicates that tests confirm the absence of the vulnerability or the successful implementation of security measures.
6. Important, Info
Important and Info are Informative findings that can help with manual assessment, understanding of application behavior or confirming certain aspects of the application, like using a certificate to sign the application.